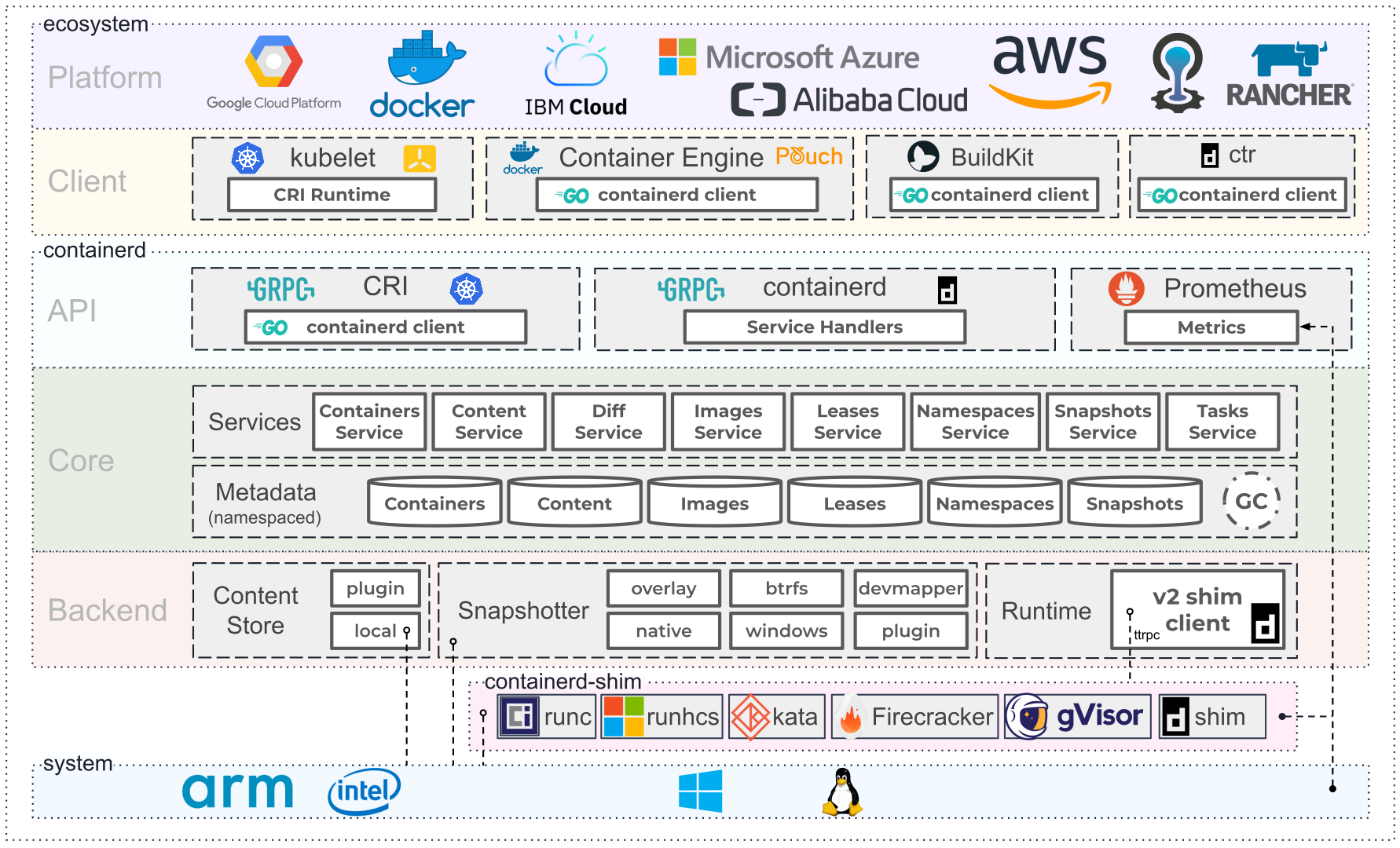
An industry-standard container runtime with an emphasis on simplicity, robustness and portability
containerd is graduating within the CNCF!
As of February 28, 2019, containerd is officially a graduated project within the Cloud Native Computing Foundation, following Kubernetes, Prometheus, Envoy, and CoreDNS. We'd like to thank the amazing containerd community for making this all possible and we're excited for the future of the project.
You can read the official announcement on the CNCF website.
🍾🎉🥳🎁
Features
- OCI Image Spec support
- Image push and pull support
- Network primitives for creation, modification, and deletion of interfaces
- Multi-tenant supported with CAS storage for global images
- OCI Runtime Spec support (aka runC)
- Container runtime and lifecycle support
- Management of network namespaces containers to join existing namespaces